Facebook Vulnerable To Serious XSS Attack
Saturday, May 31st, 2008Another XSS vulnerability has been discovered in Facebook, as reported by InformationWeek (George Hulme). The posting also links to Adrienne Felt’s Facebook security work.
|
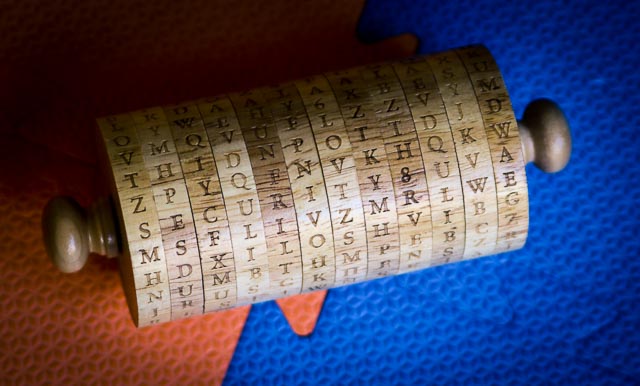
Jefferson's WheelSecurity Research at the University of Virginia |
Another XSS vulnerability has been discovered in Facebook, as reported by InformationWeek (George Hulme). The posting also links to Adrienne Felt’s Facebook security work.
Our upcoming USENIX Security Symposium paper is now available: Reverse-Engineering a Cryptographic RFID Tag by Karsten Nohl, David Evans, Starbug, and Henryk Plötz.
The paper describes the methods used to reverse engineering the encryption on the Mifare Classic RFID tag and some of the things we learned by doing it. Karsten Nohl will present the paper at the USENIX Security Symposium in San Jose on July 31.
Abstract
The security of embedded devices often relies on the secrecy of proprietary cryptographic algorithms. These algorithms and their weaknesses are frequently disclosed through reverse-engineering software, but it is commonly thought to be too expensive to reconstruct designs from a hardware implementation alone. This paper challenges that belief by presenting an approach to reverse-engineering a cipher from a silicon implementation. Using this mostly automated approach, we reveal a cipher from an RFID tag that is not known to have a software or micro-code implementation. We reconstruct the cipher from the widely used Mifare Classic RFID tag by using a combination of image analysis of circuits and protocol analysis. Our analysis reveals that the security of the tag is even below the level that its 48-bit key length suggests due to a number of design flaws. Weak random numbers and a weakness in the authentication protocol allow for pre-computed rainbow tables to be used to find any key in a matter of seconds. Our approach of deducing functionality from circuit images is mostly automated, hence it is also feasible for large chips. The assumption that algorithms can be kept secret should therefore to be avoided for any type of silicon chip.
Nathanael Paul’s PhD dissertation has been approved! He will graduate this Sunday.
The dissertation is available here: Disk-Level Malware Detection [Abstract] [Full text: PDF, 155 pages].
Congratulations, Nate! (That is, “Dr. Paul”.) Nate is currently a post-doctoral fellow at Vrije Universiteit, Amsterdam working with Andrew Tanenbaum.
Our paper, Privacy Protection for Social Networking Platforms by Adrienne Felt and David Evans is now available [PDF]. Adrienne Felt will present the paper at the Web 2.0 Security and Privacy 2008 (in conjunction with 2008 IEEE Symposium on Security and Privacy) in Oakland, CA on May 22, 2008.
Abstract
Social networking platforms integrate third-party content into social networking sites and give third-party developers access to user data. These open interfaces enable popular site enhancements but pose serious privacy risks by exposing user data to third-party developers. We address the privacy risks associated with social networking APIs by presenting a privacy-by-proxy design for a privacy-preserving API. Our design is motivated by an analysis of the data needs and uses of Facebook applications. We studied 150 popular Facebook applications and found that nearly all applications could maintain their functionality using a limited interface that only provides access to an anonymized social graph and placeholders for user data. Since the platform host can control the third party applications’ output, privacy-by-proxy can be accomplished by using new tags and data transformations without major changes to either the platform architecture or applications.
Full paper (8 pages): [PDF]
Project Website
[Added 25 May]: Talk slides (by Adrienne Felt): [PDF]