Slashdotted: Facebook Platform Privacy
Thursday, February 7th, 2008Slashdot has an article on Adrienne Felt’s Facebook platform privacy work:
Facebook Sharing Too Much Personal Data With Application Developers.
|
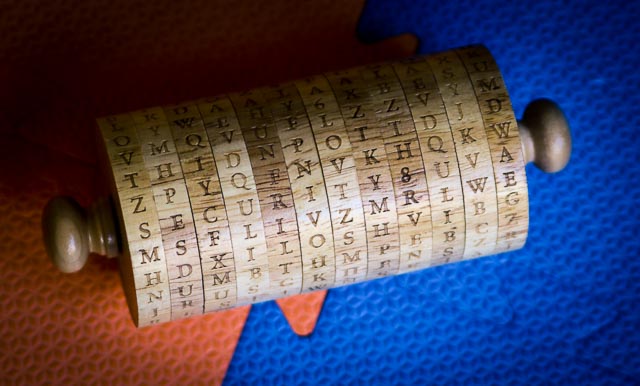
Jefferson's WheelSecurity Research at the University of Virginia |
Slashdot has an article on Adrienne Felt’s Facebook platform privacy work:
Facebook Sharing Too Much Personal Data With Application Developers.
Adrienne Felt was interviewed on KCPW Midday Utah:
Users of the popular social networking website called Facebook should be concerned about security, according to Adrienne Felt. As a senior in the School of Engineering and Applied Science at the University of Virginia where she specializes in computer security, her research shows that when users download a Facebook application – a program that allows the user to interact with other users – privacy is compromised.
The KCPW site has audio: http://www.kcpw.org/article/5281. Its quite an in-depth interview (about 20 minutes long).
I (David Evans) was interviewed for this story on NBC 29 news about a lawsuit challenging the use of DREs (software-only) voting machines as unconstitutional because they do not support non-secret counting:
Should the Voting Machines be Scrapped?, WVIR (NBC 29) TV News, 4 February 2008. (Includes Video)
WCAV had a story on Adrienne Felt’s work on Facebook platform privacy risks:
UVa Student Raises Facebook Security Concerns, WCAV TV 19 News, Charlottesville, VA. (Includes a video clip from the newscast)
Many use the social networking site Facebook without ever thinking about security but you could be leaving yourself vulnerable anytime you share music or play a game. Facebook applications are not necessarily from Facebook.
UVa Today has an article about Adrienne Felt’s work on the privacy risks of the Facebook platform:
U.Va. Engineering School Student Probes Facebook’s Vulnerabilities, UVa Today, January 30, 2008.
Here are a few excerpts:
Facebook, the social networking platform that has redefined communications, has millions of users. According to University of Virginia computer science major Adrienne Felt, all of these users should be concerned about security.
Felt, a fourth-year student in the School of Engineering and Applied Science at U.Va., leads a research project on privacy issues surrounding social networking platforms and is investigating the information sharing that occurs when users download a Facebook application — a program that allows the user to interact with other users in interesting ways, from sharing music to playing games.
Although these applications add variety to a Facebook user’s profile page, they also increase the user’s vulnerability. Here’s how: anyone with an account on Facebook can create an application. Although this application appears as if it is part of Facebook’s platform, it is actually running on application developer’s server. When a user installs an application, that application’s developer is given the ability to see everything the user can see — name, address, friends’ profiles, photos, etc.
…
Felt’s goal is to make users more aware of how their private information is being used — and to close this privacy loophole.
She has developed a privacy-by-proxy system — a way for Facebook to hide the user’s private information, while still maintaining the applications’ functionalities. Under Felt’s system, at the point at which the Facebook server is communicating with the application developer’s server, the Facebook server would provide the outside server with a random sequence of letters instead of the user’s name (and other personal information).
Felt is working on refining the privacy-by-proxy design and building a prototype implementation. “This is the first step,” she said. “Hopefully, the research findings and proposed solution will trigger more responsible privacy and information management policies from social networking sites and will better inform users.”
The full article also includes an audio clip.
[Added 2 March] There is an audio version of this story on The Oscar Show: Privacy and Facebook, 27 February 2008.
Karsten Nohl, in collaboration with Starbug and Henryk Plötz, has reverse-engineered the encryption algorithm used in Mifare Classic RFID tags, and identified several serious weaknesses in the ciper design and the way it generated random numbers. Mifare tags are used in several large public transportation systems including London Transport’s Oyster cards, and the Dutch government was planning to used them for the nationwide OV-Chipkaart system, but is reconsidering this in light of the revealed security weaknesses. The work involved reverse engineering the cipher from images of its hardware implementation.
The results were announced at the Chaos Communication Congress (December 28). Here’s Karsten’s talk (including a link to a video): Mifare: Little Security, Despite Obscurity.
Some posts about this work include:
Karsten will also be giving a talk about this work at the RFID Security Workshop at Johns Hopkins University, January 23-24.